

How to Measure the Impact of Phishing Training

You can implement all the cybersecurity measures you want, but how do you know they work? Phishing training is an excellent tool to teach your employees to recognize, avoid and report phishing attempts, protecting your team from cybersecurity threats. While you can require your team to take a security awareness course, you must be confident they have absorbed all the takeaways. You can use phishing training metrics to track your organization's security progress and see the results of your efforts.
Security Awareness Training Metrics to Track
Phishing is a highly effective form of cyberattack. You need security measures and training programs to keep your data and team safe.
While phishing awareness training can protect your team, you must have concrete data to demonstrate its success. You can evaluate your results with a few metrics from your phishing training service. These five areas will give you a complete picture of your cybersecurity awareness.
1. Training Progress
A good security awareness program will let you see your employees' progress with their training. Monitor people's headway and use regular assessments to test their skills. If you see knowledge scores increasing and more team members completing training modules, you'll know your staff is paying attention to cybersecurity and absorbing the information they need.
2. Simulation Results
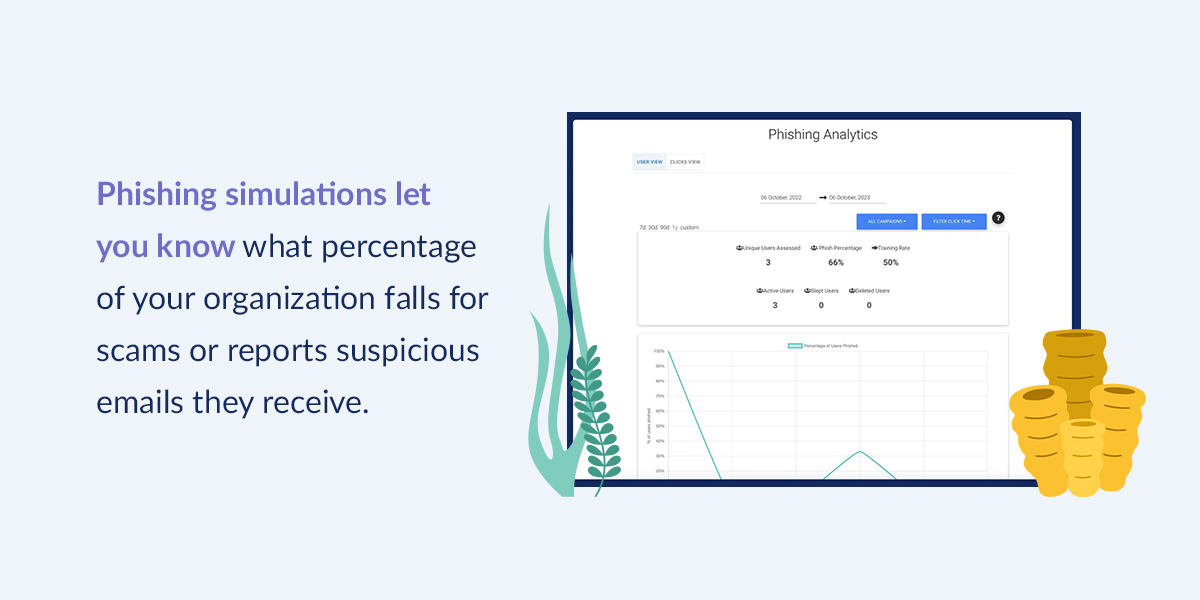
Phishing simulations let you know what percentage of your organization falls for scams or reports suspicious emails they receive. You can see your team's phishing awareness improving by tracking these results over time,
3. Response Time
Look at your incident response time scores throughout training — this metric tells you if your team is responding more quickly and effectively to cyber threats.
4. Incident Trends
If you see a decrease in security incidents since starting awareness training, this can be a sign your cybersecurity measures and training are working. The more people you educate, the better prepared they'll be to prevent security incidents.
5. User Feedback
Your team is a valuable resource for reducing cybersecurity risks and threats. They regularly take security awareness courses, giving them firsthand experience with the materials. Ask for their feedback on your updated security policies and instructional modules to evaluate your training's quality. What does everyone like about the exercises? Do they feel more confident in their ability to thwart phishing attempts? Where could improvements happen?
Start Seeing Cybersecurity Training Results With Phin Security
Lasting cybersecurity starts with robust security awareness training. Phin Security offers industry-leading phishing simulations, tailored training and real-time reporting and analytics to deliver results you can rely on. As experts in helping you defend against ever-changing cyber threats, we can provide your organization with the tools and data it needs to fight off phishing attempts. Partner with us today and use our tailored solutions to help you track and improve your business' security awareness and success rate.
Contact us today for a free trial and see how Phin can transform your security approach!







Leave a comment: